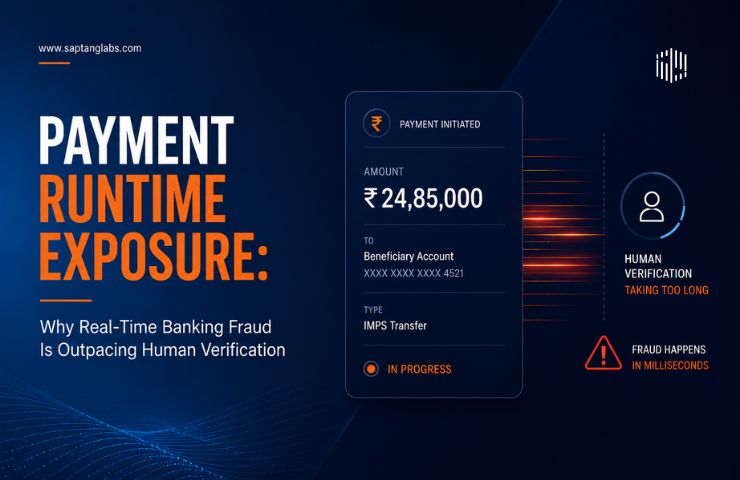
Payment Runtime Exposure: Why Real Time Banking Fraud Is Outpacing Human Verification
Payment Runtime Exposure: Why Real Time Banking Fraud Is Outpacing Human Verification TL;DR The global transition to instant payment networks has created a critical vulnerability known as Payment Runtime Exposure, which represents the microscopic window of time where a digital transaction is processed and irrevocably settled. Because these real time transactions settle in milliseconds, traditional fraud prevention methods that